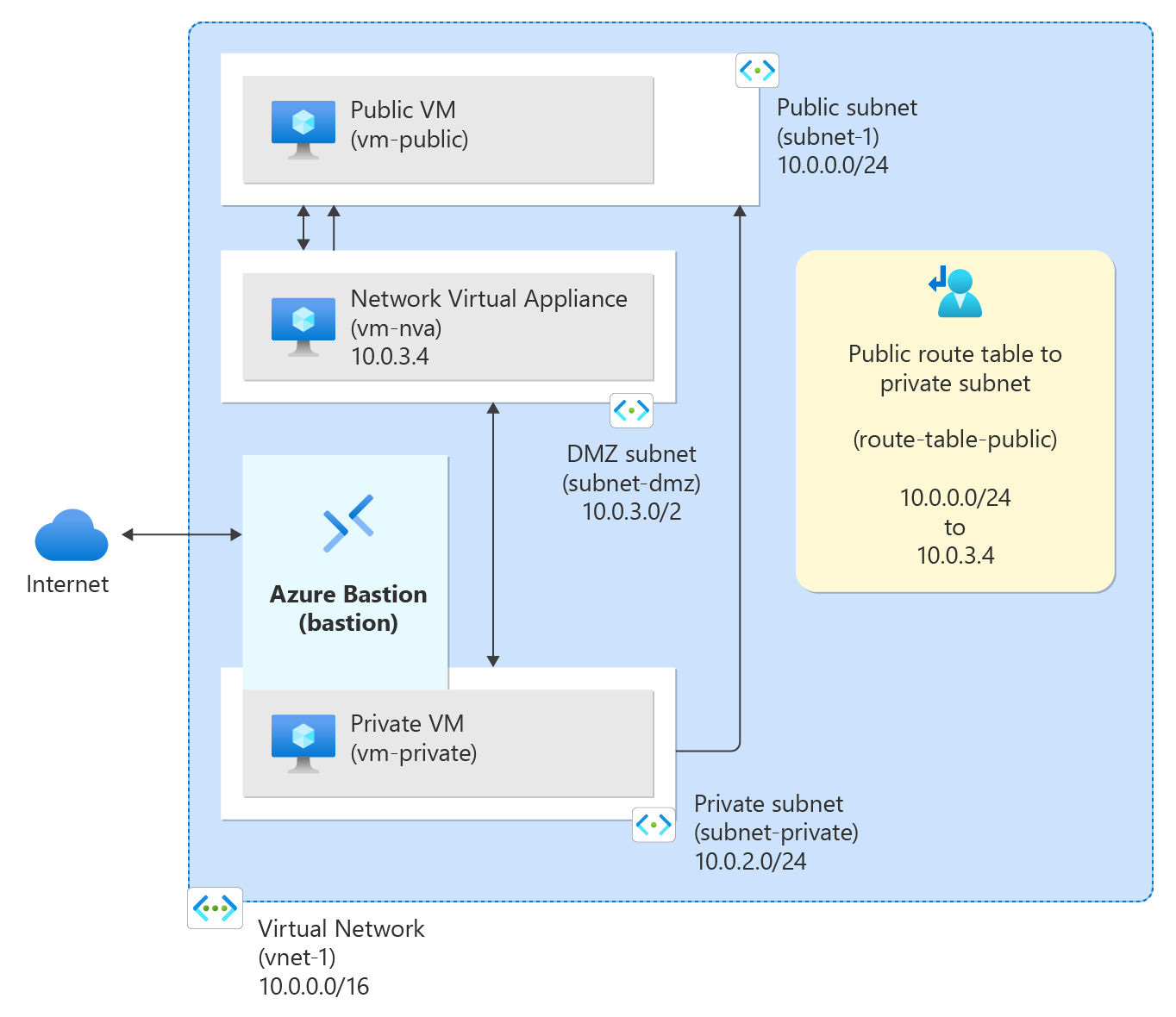
Tutorial: Route network traffic with a route table
Azure routes traffic between all subnets within a virtual network, by default. You can create your own routes to override Azure's default routing. Custom routes are helpful when, for example, you want to route traffic between subnets through a network virtual appliance (NVA).
In this tutorial, you learn how to:
- Create a virtual network and subnets
- Create an NVA that routes traffic
- Deploy virtual machines (VMs) into different subnets
- Create a route table
- Create a route
- Associate a route table to a subnet
- Route traffic from one subnet to another through an NVA
Prerequisites
- An Azure account with an active subscription. You can create an account for free.
Create subnets
A DMZ and Private subnet are needed for this tutorial. The DMZ subnet is where you deploy the NVA, and the Private subnet is where you deploy the virtual machines that you want to route traffic to. The subnet-1 is the subnet created in the previous steps. Use subnet-1 for the public virtual machine.
Create a virtual network and an Azure Bastion host
The following procedure creates a virtual network with a resource subnet, an Azure Bastion subnet, and a Bastion host:
In the portal, search for and select Virtual networks.
On the Virtual networks page, select + Create.
On the Basics tab of Create virtual network, enter, or select the following information:
Setting Value Project details Subscription Select your subscription. Resource group Select Create new.
Enter test-rg for the name.
Select OK.Instance details Name Enter vnet-1. Region Select East US 2. 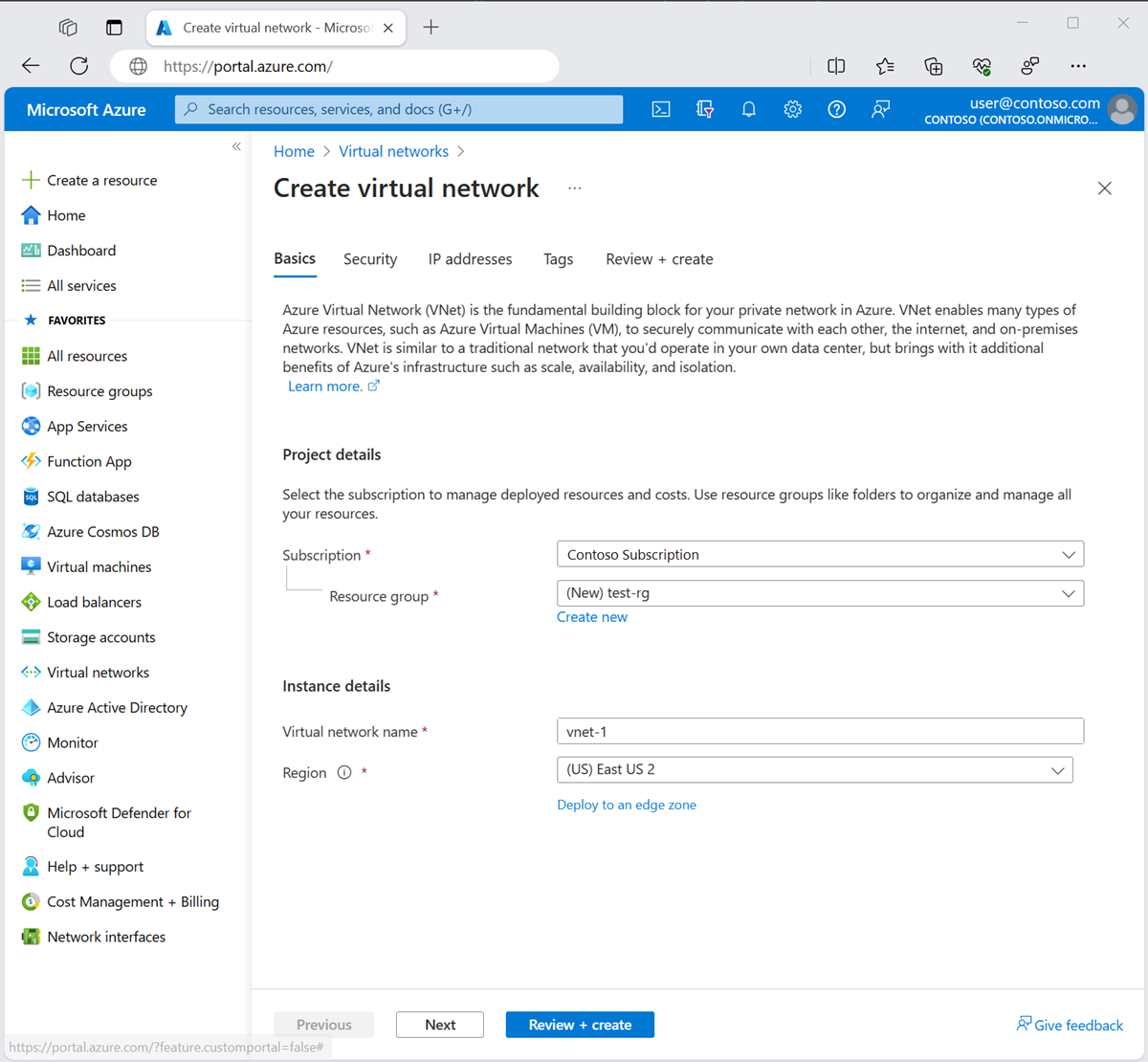
Select Next to proceed to the Security tab.
In the Azure Bastion section, select Enable Azure Bastion.
Bastion uses your browser to connect to VMs in your virtual network over Secure Shell (SSH) or Remote Desktop Protocol (RDP) by using their private IP addresses. The VMs don't need public IP addresses, client software, or special configuration. For more information, see What is Azure Bastion?.
In Azure Bastion, enter or select the following information:
Setting Value Azure Bastion host name Enter bastion. Azure Bastion public IP address Select Create a public IP address.
Enter public-ip-bastion in Name.
Select OK.
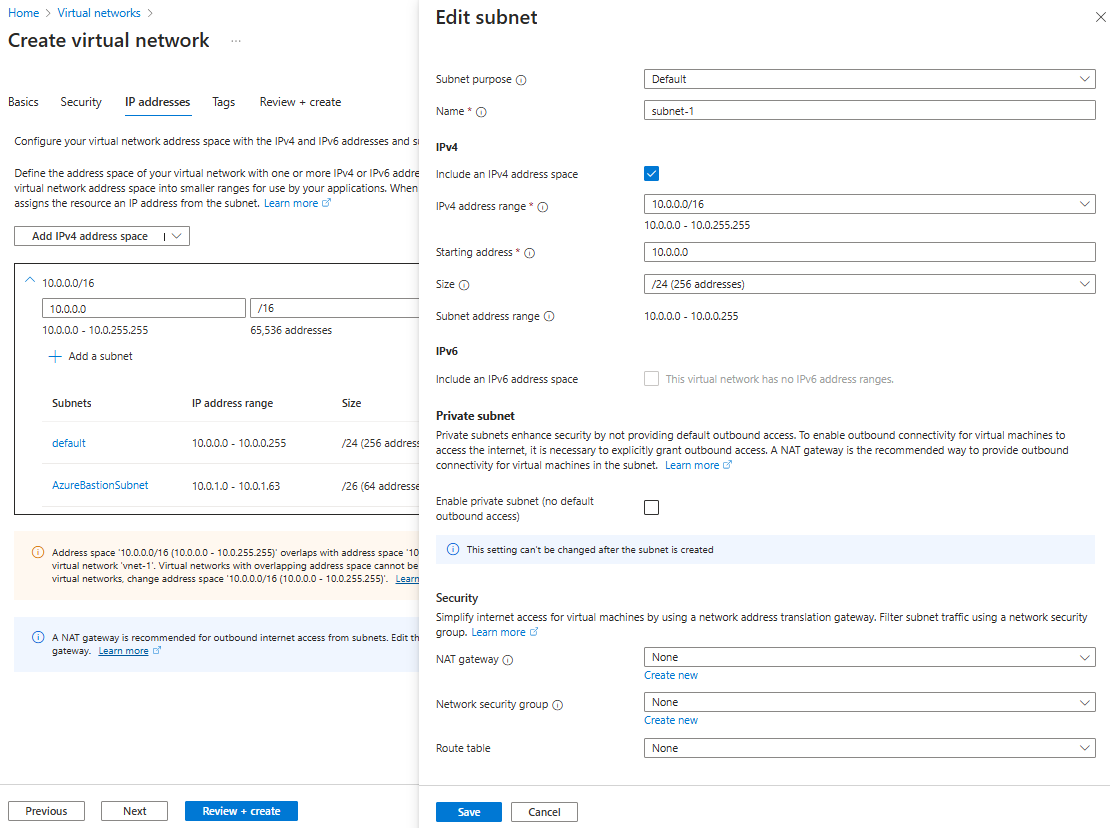
Select Next to proceed to the IP Addresses tab.
In the address space box in Subnets, select the default subnet.
In Edit subnet, enter or select the following information:
Setting Value Subnet purpose Leave the default of Default. Name Enter subnet-1. IPv4 IPv4 address range Leave the default of 10.0.0.0/16. Starting address Leave the default of 10.0.0.0. Size Leave the default of /24 (256 addresses). Select Save.
Select Review + create at the bottom of the window. When validation passes, select Create.
In the search box at the top of the portal, enter Virtual network. Select Virtual networks in the search results.
In Virtual networks, select vnet-1.
In vnet-1, select Subnets from the Settings section.
In the virtual network's subnet list, select + Subnet.
In Add subnet, enter or select the following information:
Setting Value Subnet purpose Leave the default of Default. Name Enter subnet-private. IPv4 IPv4 address range Leave the default of 10.0.0.0/16. Starting address Enter 10.0.2.0. Size Leave the default of /24 (256 addresses). 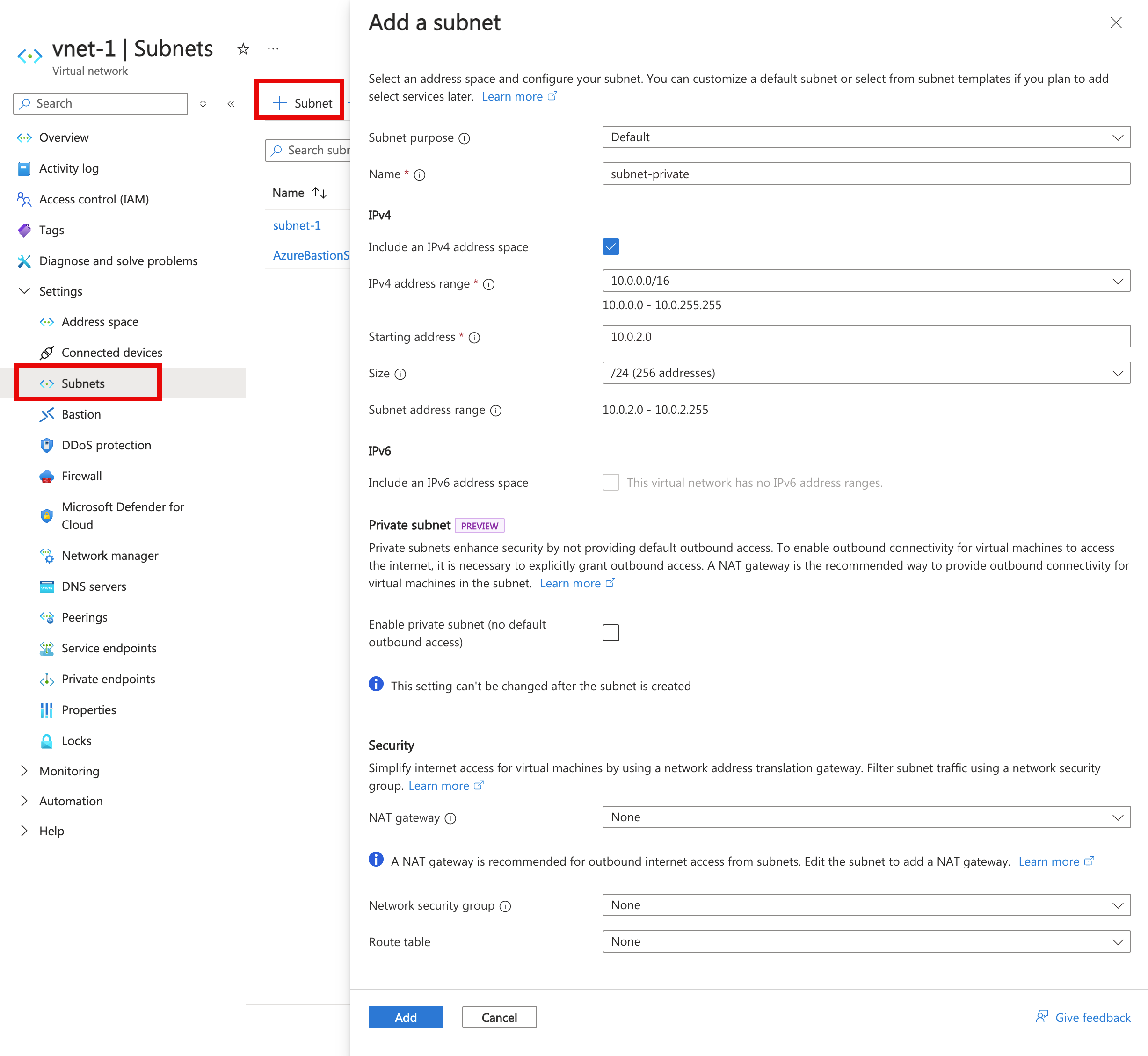
Select Add.
Select + Subnet.
In Add subnet, enter or select the following information:
Setting Value Subnet purpose Leave the default of Default. Name Enter subnet-dmz. IPv4 IPv4 address range Leave the default of 10.0.0.0/16. Starting address Enter 10.0.3.0. Size Leave the default of /24 (256 addresses). 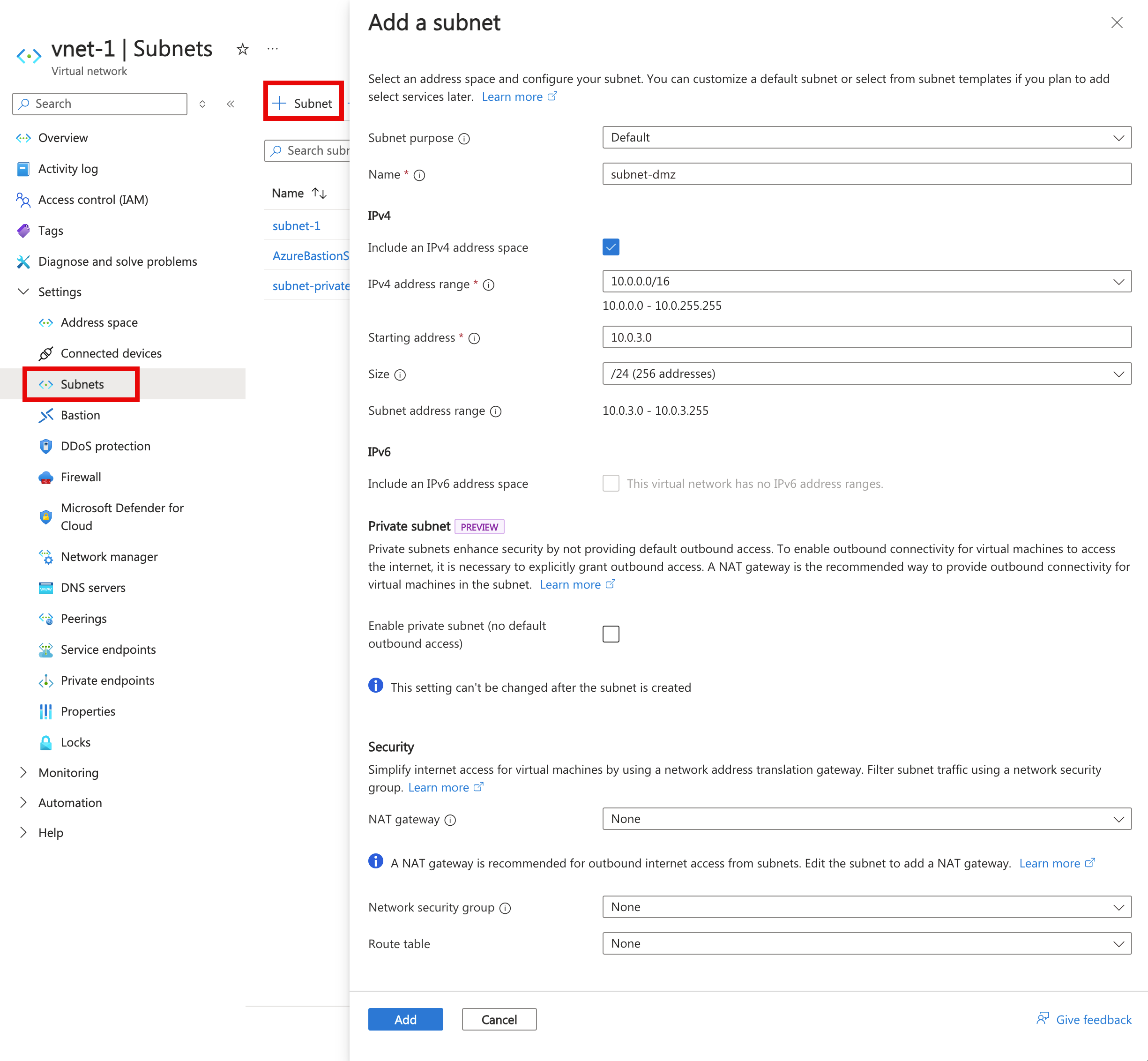
Select Add.
Create an NVA virtual machine
Network virtual appliances (NVAs) are virtual machines that help with network functions, such as routing and firewall optimization. In this section, create an NVA using an Ubuntu 24.04 virtual machine.
In the search box at the top of the portal, enter Virtual machine. Select Virtual machines in the search results.
Select + Create then Azure virtual machine.
In Create a virtual machine enter or select the following information in the Basics tab:
Setting Value Project details Subscription Select your subscription. Resource group Select test-rg. Instance details Virtual machine name Enter vm-nva. Region Select (US) East US 2. Availability options Select No infrastructure redundancy required. Security type Select Standard. Image Select Ubuntu Server 24.04 LTS - x64 Gen2. VM architecture Leave the default of x64. Size Select a size. Administrator account Authentication type Select Password. Username Enter a username. Password Enter a password. Confirm password Reenter password. Inbound port rules Public inbound ports Select None. Select Next: Disks then Next: Networking.
In the Networking tab, enter or select the following information:
Setting Value Network interface Virtual network Select vnet-1. Subnet Select subnet-dmz (10.0.3.0/24). Public IP Select None. NIC network security group Select Advanced. Configure network security group Select Create new.
In Name enter nsg-nva.
Select OK.Leave the rest of the options at the defaults and select Review + create.
Select Create.
Create public and private virtual machines
Create two virtual machines in the vnet-1 virtual network. One virtual machine is in the subnet-1 subnet, and the other virtual machine is in the subnet-private subnet. Use the same virtual machine image for both virtual machines.
Create public virtual machine
The public virtual machine is used to simulate a machine in the public internet. The public and private virtual machine are used to test the routing of network traffic through the NVA virtual machine.
In the search box at the top of the portal, enter Virtual machine. Select Virtual machines in the search results.
Select + Create then Azure virtual machine.
In Create a virtual machine enter or select the following information in the Basics tab:
Setting Value Project details Subscription Select your subscription. Resource group Select test-rg. Instance details Virtual machine name Enter vm-public. Region Select (US) East US 2. Availability options Select No infrastructure redundancy required. Security type Select Standard. Image Select Ubuntu Server 24.04 LTS - x64 Gen2. VM architecture Leave the default of x64. Size Select a size. Administrator account Authentication type Select Password. Username Enter a username. Password Enter a password. Confirm password Reenter password. Inbound port rules Public inbound ports Select None. Select Next: Disks then Next: Networking.
In the Networking tab, enter or select the following information:
Setting Value Network interface Virtual network Select vnet-1. Subnet Select subnet-1 (10.0.0.0/24). Public IP Select None. NIC network security group Select None. Leave the rest of the options at the defaults and select Review + create.
Select Create.
Create private virtual machine
In the search box at the top of the portal, enter Virtual machine. Select Virtual machines in the search results.
Select + Create then Azure virtual machine.
In Create a virtual machine enter or select the following information in the Basics tab:
Setting Value Project details Subscription Select your subscription. Resource group Select test-rg. Instance details Virtual machine name Enter vm-private. Region Select (US) East US 2. Availability options Select No infrastructure redundancy required. Security type Select Standard. Image Select Ubuntu Server 24.04 LTS - x64 Gen2. VM architecture Leave the default of x64. Size Select a size. Administrator account Authentication type Select Password. Username Enter a username. Password Enter a password. Confirm password Reenter password. Inbound port rules Public inbound ports Select None. Select Next: Disks then Next: Networking.
In the Networking tab, enter or select the following information:
Setting Value Network interface Virtual network Select vnet-1. Subnet Select subnet-private (10.0.2.0/24). Public IP Select None. NIC network security group Select None. Leave the rest of the options at the defaults and select Review + create.
Select Create.
Enable IP forwarding
To route traffic through the NVA, turn on IP forwarding in Azure and in the operating system of vm-nva. When IP forwarding is enabled, any traffic received by vm-nva that's destined for a different IP address, isn't dropped and is forwarded to the correct destination.
Enable IP forwarding in Azure
In this section, you turn on IP forwarding for the network interface of the vm-nva virtual machine.
In the search box at the top of the portal, enter Virtual machine. Select Virtual machines in the search results.
In Virtual machines, select vm-nva.
In vm-nva, expand Networking then select Network settings.
Select the name of the interface next to Network Interface:. The name begins with vm-nva and has a random number assigned to the interface. The name of the interface in this example is vm-nva313.
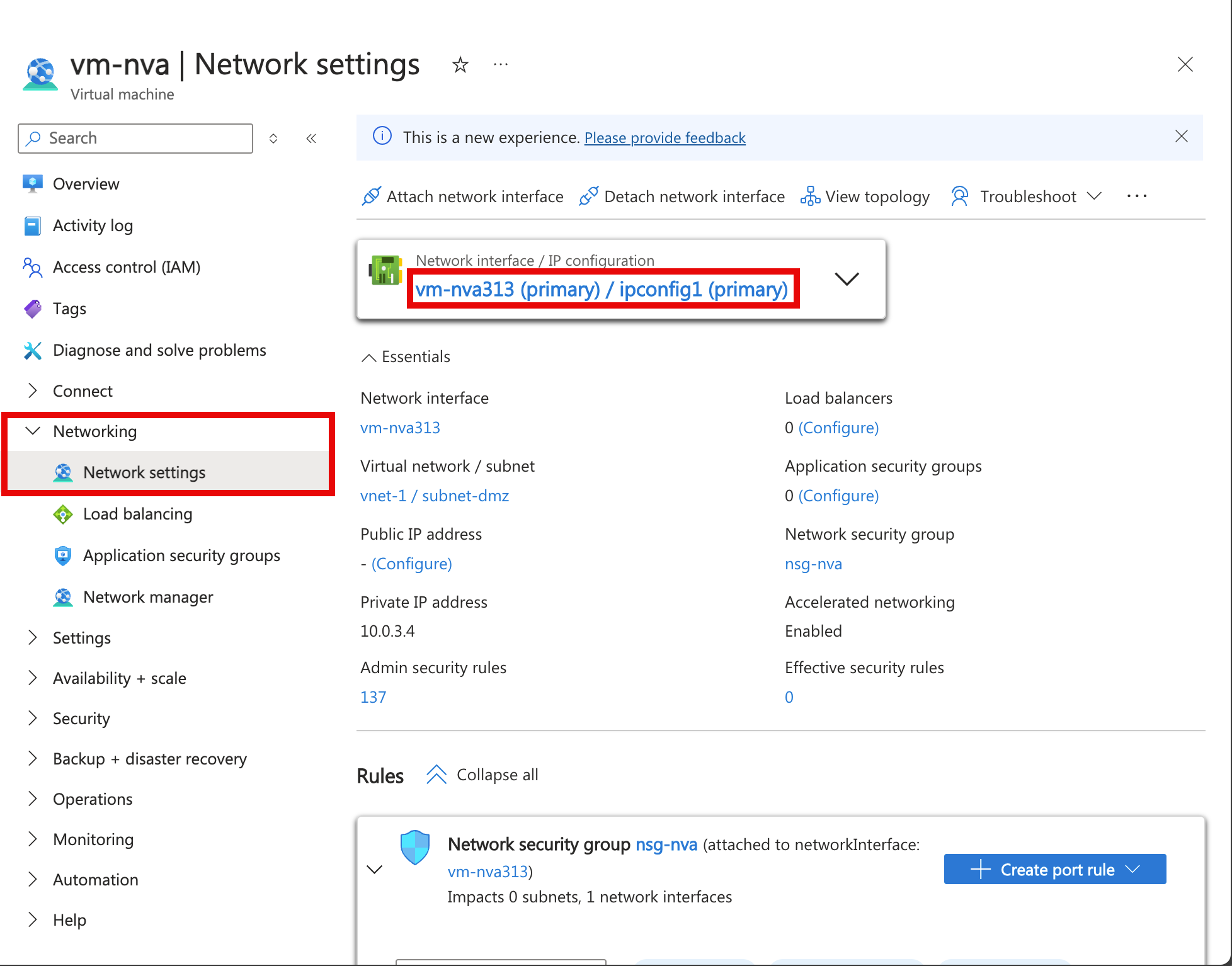
In the network interface overview page, select IP configurations from the Settings section.
In IP configurations, select the box next to Enable IP forwarding.
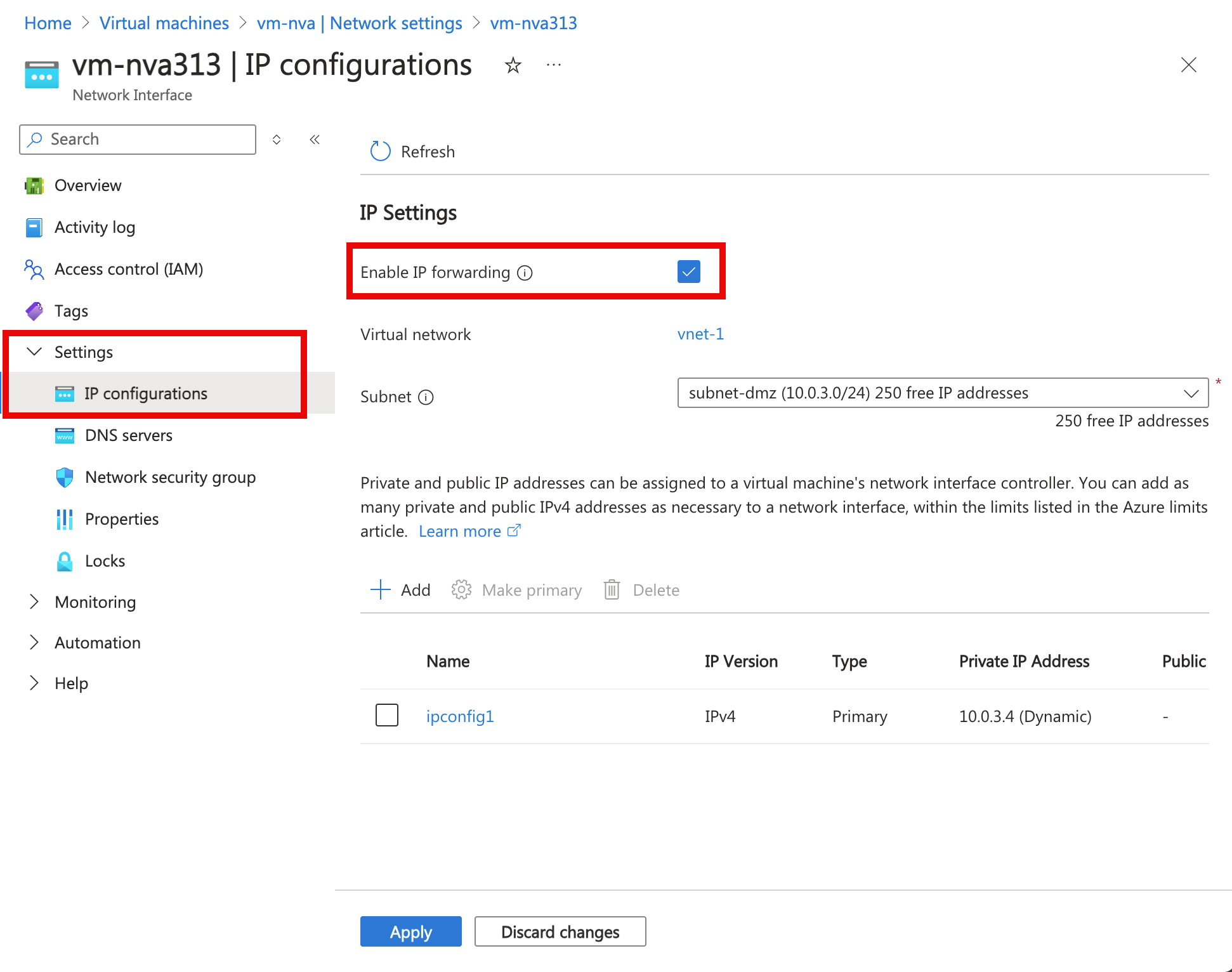
Select Apply.
Enable IP forwarding in the operating system
In this section, turn on IP forwarding for the operating system of the vm-nva virtual machine to forward network traffic. Use the Azure Bastion service to connect to the vm-nva virtual machine.
In the search box at the top of the portal, enter Virtual machine. Select Virtual machines in the search results.
In Virtual machines, select vm-nva.
Select Connect, then Connect via Bastion in the Overview section.
Enter the username and password you entered when the virtual machine was created.
Select Connect.
Enter the following information at the prompt of the virtual machine to enable IP forwarding:
sudo vim /etc/sysctl.confIn the Vim editor, remove the
#from the linenet.ipv4.ip_forward=1:Press the Insert key.
# Uncomment the next line to enable packet forwarding for IPv4 net.ipv4.ip_forward=1Press the Esc key.
Enter
:wqand press Enter.Close the Bastion session.
Restart the virtual machine.
Create a route table
In this section, create a route table to define the route of the traffic through the NVA virtual machine. The route table is associated to the subnet-1 subnet where the vm-public virtual machine is deployed.
In the search box at the top of the portal, enter Route table. Select Route tables in the search results.
Select + Create.
In Create Route table enter or select the following information:
Setting Value Project details Subscription Select your subscription. Resource group Select test-rg. Instance details Region Select East US 2. Name Enter route-table-public. Propagate gateway routes Leave the default of Yes. Select Review + create.
Select Create.
Create a route
In this section, create a route in the route table that you created in the previous steps.
In the search box at the top of the portal, enter Route table. Select Route tables in the search results.
Select route-table-public.
Expand Settings then select Routes.
Select + Add in Routes.
Enter or select the following information in Add route:
Setting Value Route name Enter to-private-subnet. Destination type Select IP Addresses. Destination IP addresses/CIDR ranges Enter 10.0.2.0/24. Next hop type Select Virtual appliance. Next hop address Enter 10.0.3.4.
This is the IP address of the vm-nva you created in the earlier steps..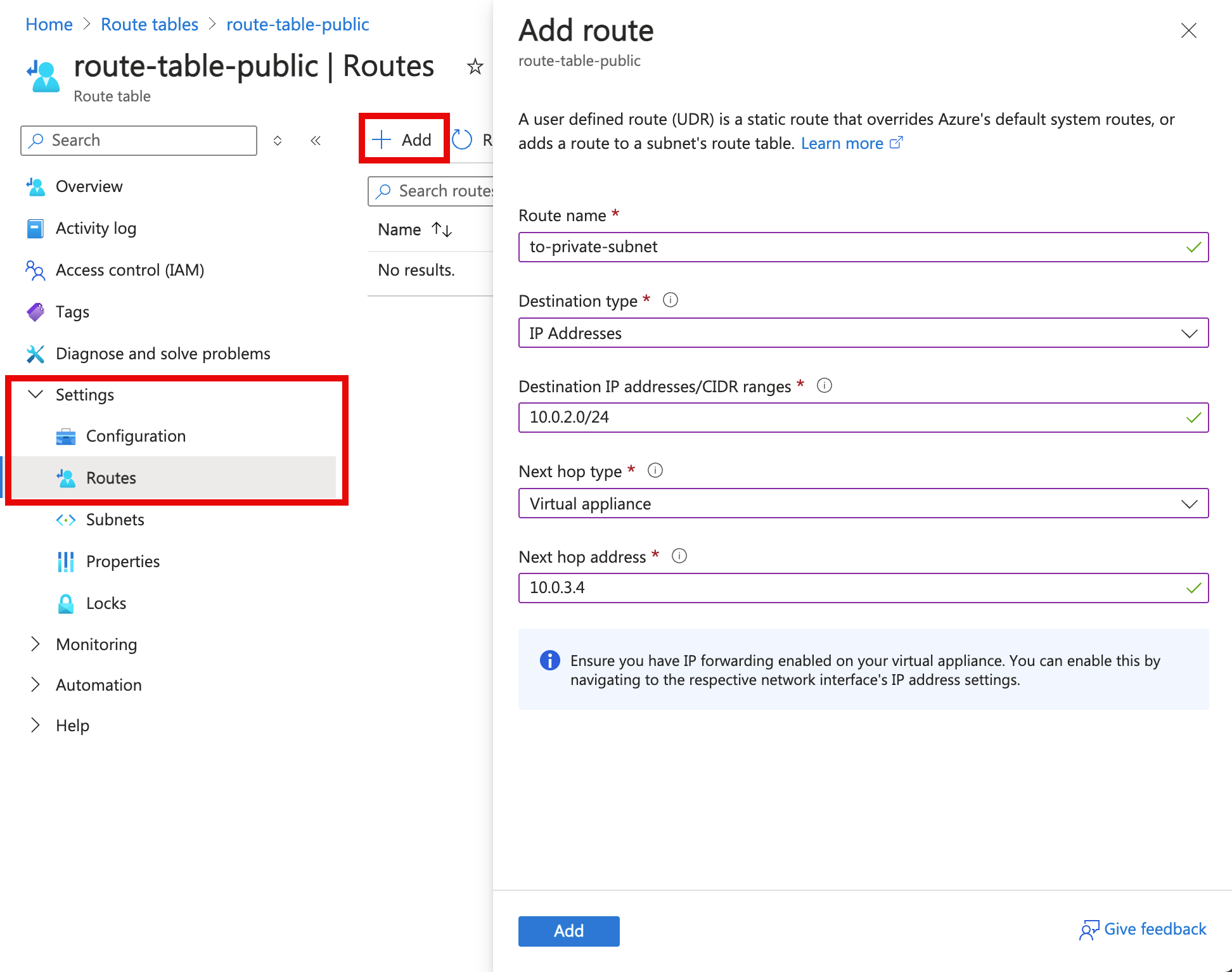
Select Add.
Select Subnets in Settings.
Select + Associate.
Enter or select the following information in Associate subnet:
Setting Value Virtual network Select vnet-1 (test-rg). Subnet Select subnet-1. Select OK.
Test the routing of network traffic
Test routing of network traffic from vm-public to vm-private. Test routing of network traffic from vm-private to vm-public.
Test network traffic from vm-public to vm-private
In the search box at the top of the portal, enter Virtual machine. Select Virtual machines in the search results.
In Virtual machines, select vm-public.
Select Connect then Connect via Bastion in the Overview section.
Enter the username and password you entered when the virtual machine was created.
Select Connect.
In the prompt, enter the following command to trace the routing of network traffic from vm-public to vm-private:
tracepath vm-privateThe response is similar to the following example:
azureuser@vm-public:~$ tracepath vm-private 1?: [LOCALHOST] pmtu 1500 1: vm-nva.internal.cloudapp.net 1.766ms 1: vm-nva.internal.cloudapp.net 1.259ms 2: vm-private.internal.cloudapp.net 2.202ms reached Resume: pmtu 1500 hops 2 back 1You can see that there are two hops in the above response for
tracepathICMP traffic from vm-public to vm-private. The first hop is vm-nva. The second hop is the destination vm-private.Azure sent the traffic from subnet-1 through the NVA and not directly to subnet-private because you previously added the to-private-subnet route to route-table-public and associated it to subnet-1.
Close the Bastion session.
Test network traffic from vm-private to vm-public
In the search box at the top of the portal, enter Virtual machine. Select Virtual machines in the search results.
In Virtual machines, select vm-private.
Select Connect then Connect via Bastion in the Overview section.
Enter the username and password you entered when the virtual machine was created.
Select Connect.
In the prompt, enter the following command to trace the routing of network traffic from vm-private to vm-public:
tracepath vm-publicThe response is similar to the following example:
azureuser@vm-private:~$ tracepath vm-public 1?: [LOCALHOST] pmtu 1500 1: vm-public.internal.cloudapp.net 2.584ms reached 1: vm-public.internal.cloudapp.net 2.147ms reached Resume: pmtu 1500 hops 1 back 2You can see that there's one hop in the above response, which is the destination vm-public.
Azure sent the traffic directly from subnet-private to subnet-1. By default, Azure routes traffic directly between subnets.
Close the Bastion session.
When you finish using the resources that you created, you can delete the resource group and all its resources.
In the Azure portal, search for and select Resource groups.
On the Resource groups page, select the test-rg resource group.
On the test-rg page, select Delete resource group.
Enter test-rg in Enter resource group name to confirm deletion, and then select Delete.
Next steps
In this tutorial, you:
Created a route table and associated it to a subnet.
Created a simple NVA that routed traffic from a public subnet to a private subnet.
You can deploy different preconfigured NVAs from the Azure Marketplace, which provide many useful network functions.
To learn more about routing, see Routing overview and Manage a route table.
To learn how to restrict network access to PaaS resources with virtual network service endpoints, advance to the next tutorial.